Ransomware Protection

Why Organizations Need Ransomware Protection
- Compromised or lost data
Once cyberattackers gain control of files during a ransomware attack, it is almost impossible to know what will happen to those records if the ransom is not paid, or even if it is paid.- Encrypted files can be left encrypted and inaccessible to the organization, or only a subset might be decrypted.
- Sensitive organizational data could be released to the public.
- Files may be posted for sale on the dark web (e.g., credit card information).
- Attackers may hold the files for other attacks (e.g., credential stuffing).
- Malware can be embedded in the files that are returned, to leave a backdoor for future attacks.
- Downtime
Nearly as damaging as the loss of data is the lack of systems availability. Often, the downtime that a ransomware attack can cause is as damaging, or even more damaging, than the impacted data.
Most organizations rely on system uptime to function. If IT environments are unavailable for an extended period of time, the results can be devastating. - More attacks
Paying ransom often only encourages more attacks—either by new hacking organizations or the ones who initiated the first attack. It also emboldens attackers to press on in their efforts. - Lost ransom money
Many ransomware attacks are targeted, and the attackers have a keen sense of how much the target organization can and will pay to retrieve its assets. Ransom demands can be very expensive, and once delivered, ransom money is almost never recouped.
In addition, paying the ransom is no guarantee that the problems will end. As noted above, there is no way to know how successful negotiations with a cybercriminal might be. - Reputational damage
Despite how the attack occurred, ransomware attacks can give customers and partners the impression that the targeted organization was at fault. Few people want to work with an organization that is perceived to be lax on security and unable to prevent criminals from breaking into the organization. In addition, ransomware attacks often impede an organization from delivering on commitments due to operational disruptions, which also negatively impacts its reputation.
Because of data breach notification laws, organizations are required to report ransomware attacks in which data has been compromised. Even in cases where a data breach is not reported, the attackers commonly make the attack public in order to pressure the organization into paying ransom.
How Ransomware Attacks Happen
The strains and approaches of ransomware continue to grow in scale and sophistication. There are a number of ways ransomware attacks happen. Following are a few of the more recent trends.
Big-Game Hunting
The more spam-like attacks that marked early ransomware campaigns, also known as “spray and pray,” are being replaced by laser-focused ones. With big-game hunting, a high-value target is selected, and a customized campaign is created to infiltrate the organization and launch the ransomware attack.
Blended Campaigns
Larger, international cybercriminal rings are using ransomware attacks as a subterfuge to cover for a bigger prize—cryptocurrency mining. The ransomware attacks serve as a revenue stream, as well as provide valuable cover for even more lucrative cryptocurrency mining.
Cyberattackers Evade Detection
- Create a backdoor for future attacks after the initial breach.
- Encrypt files slowly over a period of time.
- Launch multi-threaded attacks.
- Randomize encryption.
- Use polymorphic malware.
Cyberattackers Hamper Recovery Efforts
- Attack shared network drives and files stored in the cloud.
- Delete any files with backup extensions.
- Encrypt hard drives and master boot records.
- Target key operational infrastructure, such as email servers, web servers, applications servers, and collaboration tools.
Intelligence Gathering
In some cases, breaches are not perpetrated (at least initially) to launch a ransomware attack. Organizations have been targeted and breached by criminals who are building out an intelligence portfolio for ransomware attacks.
The information is used for attacks on the breached organization or sometimes to support attacks on others. Information gathered is used in big-game hunting attacks.
Ransomware Recovery
The first step to ransomware recovery is to be aware of the attack. Ransomware is stealthy, so once detected, an attack may have been underway for some time. Ransomware recovery requires patience, diligence, and a cool head.
When in the throes of a ransomware attack, many organizations are tempted to stop it by simply paying the ransom. Law enforcement and industry agree that this is frequently the wrong move. Paying the ransom does not ensure that the files will be decrypted and can trigger attacks by others.
Five Steps for Ransomware Recovery
- 1. Infection detection
- 2. Damage containment
- 3. Data restoration
- 4. Alerting authorities
- 5. Testing access
Data Restoration for Ransomware Recovery
Once a ransomware attack has been detected and contained, some, if not all, files will need to be restored. Data can be restored using backups or decryption.
3-2-1 Backup Best Practice
The 3-2-1 backup strategy ensures multiple copies of data are backed up and retained.
- One
Keep one copy of data offsite. - Two
Use two different storage types. For instance, if data is stored on an internal hard drive, use a secondary device such as an external drive or cloud source. - Three
Keep three copies of data: The original data copy, and at least two backups.
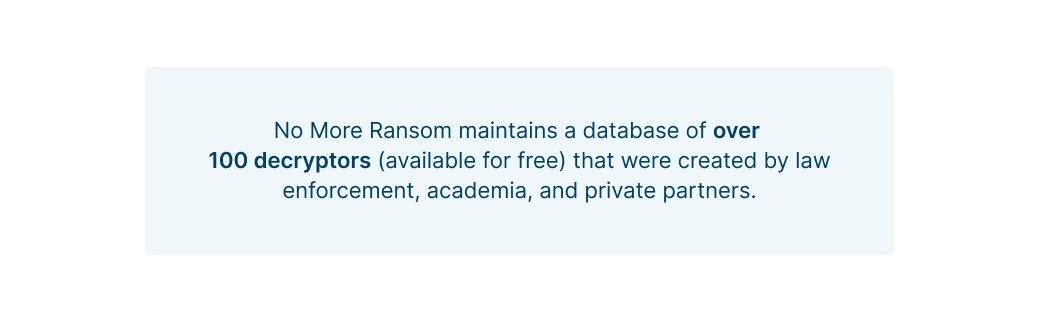
Free Decryption Tools
Law enforcement and IT security companies have joined forces to disrupt ransomware attacks.
No More Ransom is an initiative by the National High Tech Crime Unit of the Netherlands’ police, Europol’s European Cybercrime Centre, Kaspersky, and McAfee, along with nearly 200 partners worldwide. Its goal is to help victims of ransomware retrieve their encrypted data without having to pay cybercriminals.
Anti-Ransomware Strategies
While ransomware is a formidable cyberthreat, there are a number of anti-ransomware strategies that provide ransomware protection. Ransomware attacks are usually made relatively slowly, in phases, to evade detection. Following are elements that can be used as part of anti-ransomware strategies.
Continuously Train Employees
Most ransomware attacks are the result of human error—employees making mistakes. Employee training significantly reduces risks from phishing attacks and other malware. Continuous training helps build security awareness into an organizations’ culture and processes.
Avoid Paying the Ransom
Paying the ransom in the event of an attack only invites others to target organizations that pay the ransom. In addition, there are no guarantees that the attacker will decrypt files and not retain copies.
Companies that facilitate ransomware payments to cyber actors on behalf of victims, including financial institutions, cyber insurance firms, and companies involved in digital forensics and incident response, not only encourage future ransomware payment demands but also may risk violating OFAC regulations.
U.S. Treasury Office of Foreign Assets Control (OFAC)
Follow the Principle of Least Privilege
With the principle of least privilege (PoLP), users are granted only the minimum levels of access or permissions required to perform their job functions. It is considered a key step in preventing data breaches (which can lead to ransomware attacks).
The PoLP can also be applied to applications, systems, and connected devices that require privileges or permissions for access. Identity and access management (IAM) controls can help deploy and manage least privilege access across an organization—for people and devices.
Ransomware Detection
To prevent ransomware attacks, organizations need to be a step ahead of the attackers. Establishing protocols, implementing processes, and utilizing prevention tools go a long way to stopping a ransomware attack before it can do damage.
Six Tips for Ransomware Detection
- Be on the lookout for repeated suspicious login activities. A few occasional failed logins are normal, such as if a user forgets a password and tries a few that fail. When this repeatedly occurs across multiple user accounts, that could be an indicator of a potential attack. Successful logins can also be a clue—for instance, multiple successful logins from an unusual location or IP address. Or, logins that are initially performed locally, then followed by logins from different locations over a period of time, with subsequent logins coming from distances that would not be physically possible, are also indicators of someone trying to gain unauthorized access. A simple example would be a successful user login from the New York, NY area, followed by a successful user login from the Los Angeles, CA area minutes later.
- Continuously monitor for signs of test attacks. Often, small-scale attacks on a few systems will precede a full-blown ransomware attack. All attacks or suspicious incidents should be investigated as part of standard ransomware detection protocols.
- Do not forget the small devices. Despite having highly sophisticated systems in place to protect an organization’s systems and networks, ransomware detection tools leave cracks for attackers. Small devices, especially IoT devices, are regularly used as a point of entry for attackers. In fact, a fish tank was once hacked and used to break into a casino’s network.
- Implement systems to detect attempts to corrupt backups or disable security software. In addition to encrypting files, attackers sometimes corrupt backups as a way to increase pressure on organizations to pay a ransom.
- Monitor active directory and domain controllers to watch for attempts to disable them. These attacks are less automated as attackers mount sophisticated campaigns with careful pre-planning, as is done with big-game hunting.
- Watch for network scanners that are not part of the registered inventory. On occasion, an authorized user may use a network scanner for legitimate purposes, but if an unanticipated network scanner is detected, it should be investigated.
Preventing Unauthorized Access
Implement IP Whitelisting
Create a list of trusted and authorized IP addresses from which users can access the organization’s network. If someone with an untrusted IP address tries to access the network, they will be denied access. IP whitelisting also enables organizations to secure remote access to the network, including bring your own device (BYOD) environments.
Change Logins to Passphrases
Replace passwords with strings of randomized combinations of letters, numbers and symbols.
Adopt Multi-Factor Authentication
Multi-factor authentication is one of the best defenses against phishing attacks. Credentials may get stolen, but the additional layers provided with multi-factor authentication render them nearly useless.
Backup All Data
Set up systems and processes to backup all data on a regular basis. Follow the 3-2-1 strategy noted above. In the event of a ransomware attack, secure, offsite backups will provide the resiliency that’s needed for a full and rapid recovery.
Employ Threat Intelligence Services
Third parties provide access to the latest threat intelligence to provide more context for monitoring and scanning programs. This allows organizations to get ahead of ransomware attackers by identifying where some of the attacks are coming from and using that information to block incoming traffic at the organization’s firewall.
If an attack slips through, threat intelligence can help organizations respond to it quickly effectively as well as stop the attack from spreading. Use automation to take full advantage of threat intelligence.
Filter Web and Email Content
Content filtering uses software or hardware to block websites or content—stopping most malicious content, including ransomware. Pair content filtering with threat intelligence to block and quarantine known threats and suspicious content before users can access them.
Leverage Deception Tools
Set up lures, honeypots, or a distributed deception platform to identify unauthorized lateral movement. This is an effective way to discover test attacks and an active breach in progress.
Monitor Emails and File Activity
By scanning and monitoring emails, one of the primary targets for cyberattacks is protected from phishing schemes and other malware. Automated email security tools can block malicious emails before they reach users’ inboxes.
The same goes for file activity. Using tools to monitor and scan file activity can help establish a baseline for legitimate use, making it easier to identify unusual patterns that could be part of a ransomware or other attack.
Segment Networks
Divide a network into multiple segments or subnets, each acting as its own small network. Network segmentation reduces the number of users in specific zones, thereby limiting the attack surface in the event that a network is breached.
Take Advantage of Security Tools
A few must-have tools to help prevent unauthorized access are:
- Anti-malware and anti-virus software
- Data loss prevention
- Firewall
- Intrusion detection system (IDS)
- SIEM (Security Incident Event Manager)
Update All Software
Maintain an inventory of all software and create a plan to regularly install patches and updates, taking advantage of automation tools wherever possible. These often correct known vulnerabilities that ransomware attackers can and will exploit.
In addition, continuously monitor for vulnerabilities. Periodically review the software update plan to identify any issues.
Ransomware and Cryptojacking
Cryptojacking criminals use many of the same tactics as ransomware attackers to gain unauthorized access to systems. Once inside, computer processing power is used to mine for cryptocurrency.
The motivation here is that it takes an enormous amount of energy to mine for cryptocurrency. According to the Bitcoin Energy Consumption Index, one Bitcoin transaction uses as much energy as processing 100,000 Visa credit card transactions.
Oftentimes, ransomware attacks are used as a distraction. The ransomware prevention systems are set off to stop the ransomware attack, but attackers are also establishing a cryptomining program.
Commit to Ongoing Investment in Ransomware Protection
The tentacles of ransomware are deep and dangerous. Ransomware protection must be robust and take into account all parts of an organization’s IT footprint.
Ransomware protection is not a linear process or a one-time activity. It must be an ongoing investment with committed IT resources.
Egnyte has experts ready to answer your questions. For more than a decade, Egnyte has helped more than 16,000 customers with millions of customers worldwide.
Last Updated: 17th October, 2021