Ransomware Detection and Recovery
All-in-One Solution to Detect and Mitigate Ransomware Risk
Reduce Content Exposure
Centralize visibility and access to sensitive data
- Two-factor authentication
- Geo-IP controls
- Minimize data exposure
- Data-driven access
Protect Against Variants
Detect both new and known ransomware signatures
- Unusual behavior detection
- Presence of ransom-notes
- Zero-day monitoring
- Ransomware signatures
Cut Back on Downtime Costs
Bounce back faster with less disruption
- Breach reporting
- Data classification (contracts and regulations)
- Metadata descriptions
The Egnyte Solution

Prevention Against Ransomware
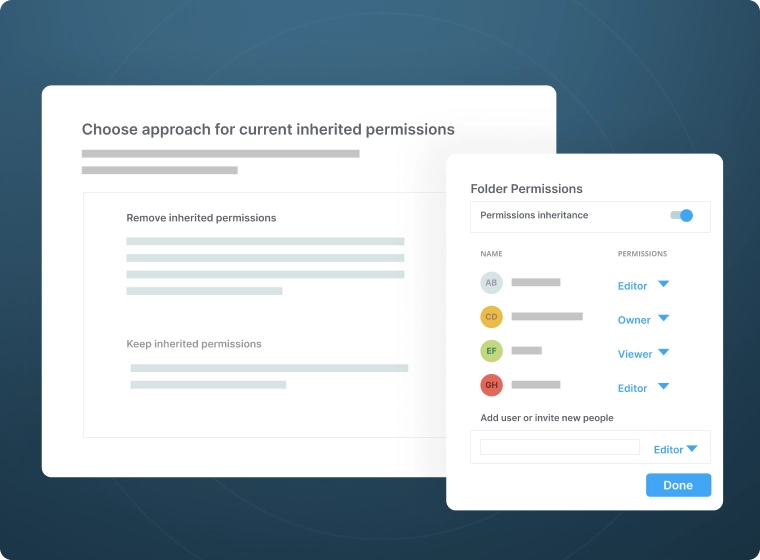
- Lock down file access with granular, least-privilege permission controls, and two-factor authentication
- Apply out-of-the-box classification patterns to locate and classify files containing sensitive information
- Minimize traffic flows to sensitive data in advance, with only a few clicks
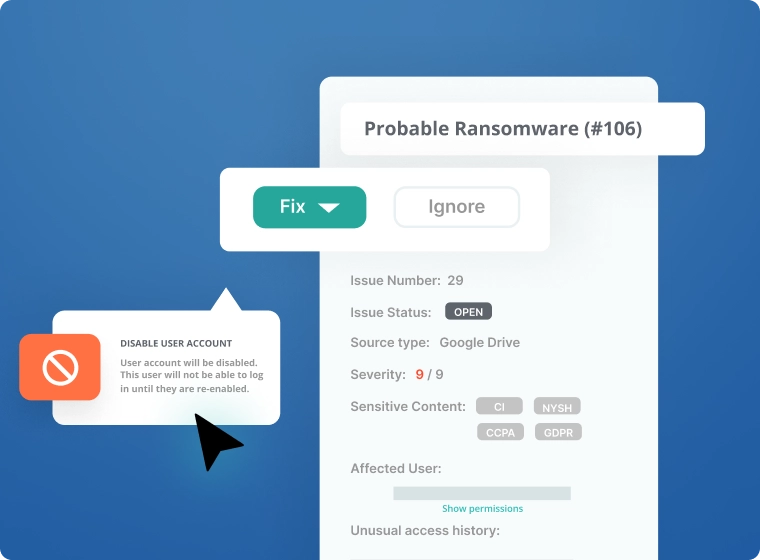
Detect Ransomware
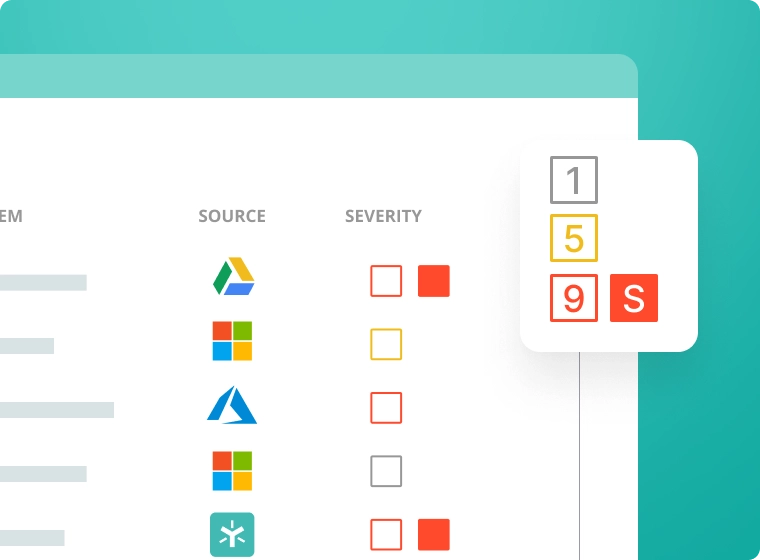
- Utilize signature-based detection to scan your folders and flag files and patterns associated with ransomware
- Identify previously unknown ransomware variants with behavioral analytics
- Access the latest, cloud-based release without worrying about maintenance
Recover from Ransomware
- Speed investigation and simplify recovery with an audit trail of compromised users, files, and data subjects/sensitive data
- Recover smarter -- roll back access judiciously across your entire organization
- Comply with GDPR notification requirements with built-in breach reporting
An Expert Team Behind You
- Count on the latest advances in data protection and ransomware detection with a dedicated team of experts
- Leverage proprietary machine learning models designed and trained specifically to fight ransomware
- Rely on fast-acting partners that ensure a smooth recovery
Faster Time to Value
Powered by Egnyte Intelligence
Learn more about Egnyte’s content intelligence engine, which includes:
- GPT-powered models allowing users to "converse" with private data sets in natural language
- Predictive models for content classification, entity extraction and unusual behavior detection
- Connected workflows such as automated labeling, security issue remediation, and human-driven review/approval tasks
The Power of Many Tools In One Turnkey Platform
Business
- Secure file sharing
- Ransomware protection
- Integrations with leading apps
- Real-time co-editing on web, desktop and mobile
Ultimate
- AI Assistant, AI Search, Model Selector
- AI Agents, Agent Builder, AI Workflows
- PDF markup and e-signature
- Sensitive data classification
- Snapshot & recovery (90-days)
Start Protecting Your Content with Egnyte Today
Chat with SpecialistFAQs
Yes, there’s a strong correlation between users clicking on phishing emails and the initiation of successful ransomware attacks. For that reason, companies should conduct regular cybersecurity awareness training for all of their users and utilize proven ransomware detection tools like Egnyte.
The 3-2-1 Rule for data backup dictates that there should be a minimum of three copies of important data, on at least two different media types, with at least one of those copies stored off-site. In addition, experts recommend that at least one copy of the backup be intentionally kept offline and inaccessible from your network. By following such an approach, an immutable copy of your backups will be available, even if an attacker gains administrative privileges, to fast-track ransomware recovery.
An effective threat intelligence program for ransomware detection and prevention consolidates threat indicators from diverse sources, eliminates duplicates, and filters noise to prioritize real threats. It provides security operations teams with clear response recommendations, automates identification of new threats, generates alerts, shares intelligence seamlessly with existing security solutions, and identifies gaps across systems and processes.
7 data recovery refers to comprehensive data recovery software that enables companies to recover mission-critical files under nearly any condition. Egnyte refers to this capability as snapshot ransomware recovery. Watch this video to learn more.
The five steps for ransomware recovery include:
- Infection detection: In this stage, ransomware detection tools like Egnyte are utilized to inform organizations of potential infection.
- Damage containment: This can involve revoking impacted users’ access or taking vulnerable systems offline to prevent further infection.
- Data restoration: Ransomware detection and recovery solutions are used to restore company data and regain users’ productivity.
- Alerting authorities: Although each ransomware attack scenario is unique, it’s important to involve your legal counsel, cyber insurance provider, and relevant authorities as soon as an attack occurs. A current incident response (IR) plan should also be on file, so that key stakeholders know their roles when a cyber-attack occurs.
- Testing access: In the final stage, you should confirm that users have regained access to all of their data and document which of your IR activities could have been handled more effectively. You should conduct an attack ‘post-mortem’ to prevent similar attacks in the future.
Although virtual private networks (VPNs) can be useful when you’re accessing a network from a high-risk location like an airplane or a public coffee shop, they were never designed for ransomware identification. Instead, you should consider a ransomware detection and removal solution like Egnyte.
The three main ransomware detection types are:
- Signature-based malware detection, which analyzes files for malicious file extensions that are indicative of ransomware.
- Artifact-based detection, where files are scanned against content sources for known ransom notes.
- Behavioral-based anomaly detection, which analyzes users’ activity to identify ransomware, including encryption and renaming of the files they access.
Egnyte supports all three of those detection types.
Although the exact cause of a ransomware infection differs from attack to attack, the primary cause of ransomware infection is human error. Specifically, many ransomware attacks result from users clicking on phishing emails. For that reason, it’s important to conduct ongoing cybersecurity awareness training for all of your users. Learn more about preventing phishing attacks in this article.

