Best Practice for Secure Remote Work
Let’s jump in and learn:
- What Is Meant by Secure Remote Access?
- Examples of How Secure Remote File Access Is Used
- Technologies That are Used for Secure Remote File Access
- Remote File Access and Business Continuity
- Secure Remote File Access to Internal File Shares
- Secure Remote Access from Anywhere
- Why Zero Trust Network Access (ZTNA) vs. VPN for Secure Remote File Access
- How Can Your Organization Share Files Remotely
- Why Secure Remote File Access Is Important
What Is Meant by Secure Remote Access?
Secure remote file access is the ability of a user to connect to an internal network, applications, and resources from outside. It is most commonly used by organizations to accommodate remote workers, vendors and partners. Secure remote file access gives users the ability to tap into file stores from any location using authorized credentials and authentication processes.

Secure remote file access relies on a combination of security solutions and processes to protect an organization’s network and digital assets, both on-premises and cloud-based, to prevent the loss of sensitive data. It is important to note that secure remote file access is not just one technology, such as a VPN, it is a mesh of security strategies with centralized control that are integrated to effectively balance protection and availability.
Examples of How Secure Remote File Access Is Used
With the ubiquity of connected devices and the mass move of workforces to home offices, an organization’s workers are no longer sequestered to a single location using an internal network. Now, employees routinely connect to their internal network and access sensitive data from remote locations. Traditional access security systems are not designed to ensure secure access. A new breed of secure remote file access systems offers a mix of integrated technologies that give employees and other verified users access from anywhere, on any device, at any time—safely and securely.
Most of an organization’s users do work outside of offices. Secure remote file access helps workers who need to securely log in to a device or system that is connected to the organization's network in the office while working from a personal device at home. In some cases, managers use secure remote file access to find out what their employees are looking at on their company devices. IT personnel often use remote access to troubleshoot technical problems from afar.
Technologies That are Used for Secure Remote File Access
Cloud access security brokers (CASBs)
The cloud is a critical resource for remote workforces, enabling secure remote file access regardless of location, which improves productivity, collaboration, and overall satisfaction. A cloud access security broker (CASB) ensures that all cloud-based usage is secure. A CASB can be used to protect on-premises or cloud-based software. It sits between a cloud service consumer and a cloud service provider and enforces an organization's security policies whenever cloud-resident data is accessed.
Desktop sharing
With desktop sharing, real-time secure remote file access is granted to another user on a separate device.
Endpoint security
Endpoint security verifies that desktop protections and enforces policies that define how remote devices (e.g., mobile devices, laptops, desktops, IoT devices) are to be used in the organization’s systems This includes ensuring that antivirus and firewall software, are in place and properly configured, patches are applied to systems and software, malicious processes are not running, and ensuring that confidential data is not cached.
Friendly net detection (FND)
This technology allows a device to automatically recognize "friendly networks.”
Network access control (NAC)
Also called network admission control, network access control is a method to bolster security, increase visibility, and reduce risk. Network access controls prevent unauthorized users and devices from gaining access to a network using a combination of tools, including two-factor authentication (2FA), endpoint security, user authentication, and network security policy education and enforcement.
Privileged access management (PAM)
This set of tools secures, monitors, and manages access to an organization’s data from privileged accounts. Privileged access management uses a blend of people, processes, and technology to protect against unauthorized access.
SD-WAN
A software-defined wide area network (SD-WAN) is a programmatically configured and managed WAN. It provides secure remote file access with a network overlay that enables IT to remotely configure, manage, monitor, and secure WANs. These are used in distributed organizations to connect offices, cloud services, and users across multiple locations.
Secure access service edge (SASE)
SASE is the combination of network functions and cloud-native network security services (e.g., CASB, FWaaS, ZTNA, SWG), bundled into a single, cloud-delivered service model. SASE enables secure remote file access by allowing users, systems, and endpoints to be securely connected to applications and services anywhere.
Single sign-on (SSO)
With single sign-on, secure remote file access is enabled by allowing an authenticated user to access select applications and resources with one set of login credentials.
Virtual private network (VPN)
VPNs are a mainstay for secure remote file access. They allow remote users to use a public internet connection to connect to a private network through an encrypted tunnel.
Remote File Access and Business Continuity
Secure remote file access is critical for business continuity in the event of a disaster. By giving users the ability to access their files from outside internal networks, secure remote file access allows them to continue to work without interruption if they are unable to be in an office physically.
In any type of disaster situation, secure remote file access is a key part of business continuity plans, because it ensures that employees can access data, applications, and other digital resources as well as work with each other. The ability to support collaboration makes secure remote file access an important technology for maintaining productivity despite a disaster.
Successfully implementing a secure remote file access system requires an assessment of what users need. Remote work solution that’s best for an organization starts with understanding what users need. Taking the time to do this ensures that the infrastructure design is aligned with user requirements and delivers the optimal end-user experience. Among the considerations for a secure remote file access system are:
- What data, applications, and other resources do users need to access?
- Where is the data, that users need, located?
- What are the bandwidth requirements to support users at appropriate performance levels?
Another use case for secure remote file access is moving users’ desktops off of their desks and into a data center or cloud. Even if they are physically located in an office, they would use secure remote file access to get to the data, applications, and other resources they need to work. Options for this include the following.
- Applications and containers can be used to move some workloads into containers can increase the density of your hosted solution and expedite users’ access.
- Cloud-hosted desktops provide on-demand computing power and secure remote file access from anywhere. In addition, the deployments can be built using virtual machines, which are available in different sizes at different prices, allowing organizations to meet the specific needs of all users.
- Full virtual desktops, or virtual desktop infrastructures (VDIs), provide flexible systems that give users access to desktop operating systems hosted as virtual machines. Virtual desktops can be dedicated or offered as non-persistent desktops, (i.e., desktops that are refreshed after the initial user logs out).
- GPU-enabled virtual machines offer an alternative to blades or workstations. They use virtualization with workstations that have multiple GPUs to support users who require high-performance capabilities (e.g., those who use graphics-intensive applications), but with less hardware.
- Shared sessions enable multiple users to log into sessions hosted on a single server operating system that shares the underlying operating system and installed applications.
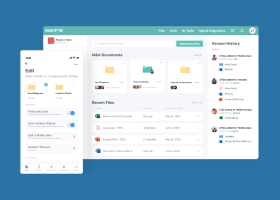
Secure Remote File Access to Internal File Shares
Simplify secure remote file server access and remote file sharing for mobile workforces with a file sharing server. These can be accessed using cloud-driven mapping of drives over HTTPS.
Secure Remote Access from Anywhere
Secure remote file access protects endpoints for all remote users and their devices. This is done in a variety of ways including:
Installing antivirus software on all endpoint devices (e.g., PC, Mac, Linux, iOS, Android)
Enforcing security policies that require all employees to follow specified protection protocols when they are to access corporate resources remotely
- Providing employees with support and training to help them use secure remote file access systems correctly to ensure optimal security
- Preventing remote access from increasing attack surface by:
- Protecting all remote desktop protocol (RDP) servers’ ports
- Not opening remote access ports unless firewalls are configured to only respond to known IP addresses
- Adopting multifactor authentication to ensure that only authorized and verified users are allowed access
- Using virtual private networks (VPN) with endpoint software that is kept up to date
- Normalizing logs and tracking security information by adjusting SIEMs and geofencing or geo-blocking features in firewalls to allow users to log gain access no matter where they are working
- Educating all users (i.e., employees, contractors, partners) with security and compliance training (e.g., reminding users not to click on any unsolicited email, attachments, or links)
- Creating and enforcing secure remote file access policies for remote users to ensure that acceptable use policies are clearly defined and followed
Why Zero Trust Network Access (ZTNA) vs. VPN for Secure Remote File Access
Zero trust network access (ZTNA), also known as the software-defined perimeter (SDP), provides secure access to applications without the need for a VPN. ZTNA is based on the premise that trust should never be implicit. Following ZTNA, access is granted on a “need-to-know,” least-privileged basis, which is defined by granular policies. Once granted, access is monitored for continuous risk assessment as recommended.
The four tenets of ZTNA are:
1. Isolate the act of providing application access from network access to reduce risks to networks (e.g., infection by compromised devices) by only granting authorized users access to applications.
2. Segmenting applications to ensure that once users are authorized, application access is granted on a one-to-one basis, with authorized users only having access to specific applications rather than the full network.
3. Take a user-to-application approach rather than a network-centric approach to security, using the internet as the new corporate network with end-to-end encrypted TLS micro-tunnels instead of MPLS.
4. Use inside-out connections from applications to users to ensure that both the network and application infrastructure are invisible to unauthorized users, by never exposing IPs to the internet to make the network impossible to find.
Several reasons commonly cited why ZTNA is a strong VPN alternative include the following.
Enhanced user experience
With ZTNA, users do not have to log in and out, because access is granted regardless of changes to network connectivity—giving users a better user experience. Latency for users is also reduced, regardless of location, providing faster access and improved productivity.
Inherent security
Because application access is decoupled from network access, networks, and applications are hidden from unauthorized users, and IPs are never exposed, which significantly reduces the attack surface and prevents lateral movement. In addition, access is only granted on a one-to-one basis only to specific applications.
Simplified management
ZTNA is all software-based, which makes it easy to deploy. Not requiring hardware, eliminates the need to install, configure, and manage appliances. In addition, because ZTNA is not IP address centric, there is no need to manage ACLs, firewall policies, or translations. With ZTNA, granular secure remote file access policies can be applied at the application and user levels. ZTNA also proves robust visibility into user activity, undiscovered applications, and the environment’s health.
ZTNA provides enhanced visibility into:
- Health monitoring of the environment
- Previously undiscovered applications
- User activity with real-time log streaming
Secure connectivity
Inside-out connectivity keeps the location of the network secret while enabling application access to individual applications within the network. VPN, connections are inbound going from the VPN client to the VPN concentrator and then directly onto the network. In addition, traffic paths from each user to each application are optimized using micro-tunnels, which are created on a per-session, on-demand basis. VPNs use a single tunnel per user, which all apps run through.
How Can Your Organization Share Files Remotely?
Secure remote file access solutions are provided in different ways depending on how what technology is used. Three commonly used technologies for secure remote file access are:
1. Desktop sharing
Connect a remote device to the host computer from an external location
2. Virtual private networks (VPNs)
Create a secure connection over the internet by encrypting data
3. Direct application access
Remotely work within individual applications on the network
Why Secure Remote File Access Is Important
For many organizations, a significant number of inbound connections now originate from remote locations. This dramatically increases risks and expands the attack surface. Secure remote file access helps mitigate risk and protect files in a number of ways including the following.
- Increased awareness of security issues
- Protection for laptops and mobile devices
- Robust endpoint protection
- Safe web access and use
- Secure access from anywhere on any device
Secure remote file access is mandatory. Any organization of any size should have a solution in place to provide secure remote file access.
Egnyte has experts ready to answer your questions. For more than a decade, Egnyte has helped more than 16,000 customers with millions of customers worldwide.
Last Updated: 16th November, 2020