Secure File Sharing Solutions

What Is Secure File Sharing?
Secure file sharing, also known as protected file sharing, is the digital transfer of links to one or more files. Transferring files, such as documents, photos, videos, and other online files, in this manner, helps protect them from unauthorized access, tampering, or theft and ensures that they are only accessed by people who have been granted permission.
With secure file sharing, sensitive information can be safely shared between different internal users or external organizations confidentially.
Most secure file sharing services address vulnerabilities by encrypting files at rest and in transit using an encryption algorithm. These protected files can then be shared within a local network, over a standard internet connection, or through a private network, such as a virtual private network or VPN.
Audit trails are also an essential part of most secure file sharing solutions. These provide documentation of all activity surrounding the transfer. Secure file sharing audit data is necessary to meet many compliance requirements, such as PCI DSS, CCPA, GDPR, SOX, HIPAA, NIST, and SOC 2.
Additional Secure File Sharing Features
Secure file sharing services offer additional security features to protect sensitive information, such as:
- Access controls based on permissions and passwords
- Link expiration capabilities
- Monitoring to identify suspicious login activity
- Multi-factor authentication
- Ransomware detection
When Secure File Sharing Is Used
There are a number of use cases that require secure file sharing. Following are several examples of when secure file sharing is used to protect files from authorized access, cyber criminals, ransomware attacks, and malware threats.
- Financial transaction
- Fundraising
- HR or personnel correspondence
- IPOs
- Legal work
- Mergers and acquisitions
- Private worker information
- Secret projects
Types of Systems Used for Secure File Sharing
Secure file sharing systems offer a variety of features, security protocols, and price points. Some are purpose-built or optimized for specific use cases. Four of the more common types of secure file systems are:
1. Cloud sharing and cloud storage solutions
2. File Transfer Protocol (FTP)
3. Peer-to-peer (P2P) networks
4. Virtual data rooms (VDRs)
How to Securely Share Files Online
Secure file sharing is usually done by encrypting the file while on users’ systems and during transit across networks. For instance, files would be transferred using 256-bit AES encryption over SSL. This is handled through secure file sharing services that manage how the files are stored, kept in sync, and distributed across devices.
Secure file sharing services have several core components, including the following:
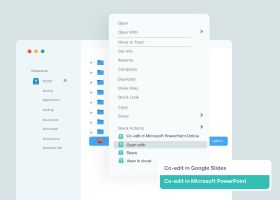
- Collaboration is used to support productive, real-time teamwork across locations.
- Content repositories with scalable and flexible storage that can manage files in cloud and on-premises environments.
- File synchronization capabilities provide consistent data access between devices or applications.
- Integrations and connectors facilitate secure file sharing across multiple locations in the cloud and on-premises.
- Support for sharing very large files without relying on cumbersome FTP servers or physical devices, such as hard drives or USB sticks.
- Unified interface to manage secure file sharing and management activities as well as to access information for compliance audit reports.
- Workflow support enables productive gain with features, such as automated feedback, approval, and e-signature.
Safe internal and external file sharing that enables seamless exchanges between internal and external stakeholders should be secured in multiple ways, including the following:
- Activity monitoring to identify suspicious login attempts or other anomalous behavior
- Encryption of data at rest and in transit
- Expiration dates for secure file transfer links to limit access to a specific period of time
- File access permissions, such as viewing, commenting, editing, or resharing files
- Integrations with other security systems, such as data loss prevention (DLP), ransomware protection, and antivirus tools
- Machine learning-powered analytics that detects anomalous activity in real-time
- Network protection inside and outside of data centers
- Notifications of downloads for each shared file
- Password protection to ensure only recipients who know the password can access the file
- Physical protections in the data centers where content is stored
- Restrictions on mass file deletion
- Version history to allow for restoring a file to a prior draft
- Virus scanning during the download process
Top 4 Benefits of Secure File Sharing
Secure file sharing services provide many benefits. The most commonly cited four high-level benefits of secure file sharing are these four.
1. Auditability
All files that are received by or sent from an organization are tracked and recorded, making it easy to investigate an incident or provide validations for compliance reports.
2. Collaboration
Users are able to easily access and share files internally and externally, as well as create and manage workflows.
3. Data security
Security gaps and governance challenges are eliminated with the access controls and other protections included with most secure file sharing systems.
4. Scalability
Secure file sharing services are designed for elasticity, supporting the changing requirements of an organization.
Additional benefits of secure file sharing include:
- Supports hybrid and remote work
- Secure file sharing addresses the needs of organizations that have employees who work either full or part-time remotely. This service allows users to access and share files of any size or type from any location (e.g., cloud storage service, corporate networks) using any connected device (e.g., desktop, laptop, phone, tablet).
- Enhanced productivity
- Secure file sharing services can make accessing and transferring files a simple, streamlined process. Productivity is enhanced, because users do not have to perform complicated and often risky tactics to share files, especially large ones. Additional productivity gains are realized with the integration of workflows for approvals, feedback, and e-signatures directly in a secure file sharing solution.
- No data migration
- Most secure file sharing systems connect directly to storage locations—on-premises or in the cloud. This eliminates the need to migrate data, which can be a time-consuming and expensive process.
- Reduced risk of shadow IT
- When a secure file sharing system is in place, users are less likely to use unapproved file sharing applications. By reducing shadow IT, an organization’s overall security posture is enhanced, and the risk of data breaches is mitigated.
Easy and Secure File Sharing for Business
A system that makes secure file sharing easy for businesses goes beyond security to provide reliable and scalable services. An effective secure file sharing solution has a number of specific features that allow it to support business requirements and improve security and productivity. Among the features that deliver easy and secure file sharing for business are the following.
Collaboration tools
Functionality that helps secure file sharing systems facilitate collaboration, according to permissions, are:
- Collaborate
- Comment
- Download
- Edit
- Share
- View
Dashboards
An easy-to-use dashboard and visibility tools are critical for making secure file sharing easy. A dashboard allows administrators to track all data flows and permissions as well as provide analytics for performance, activity, and compliance reporting.
Robust data movement
Quick connections to internal systems and the external ecosystem enable the secure transfer of data in a way that meets business compliance requirements. This is accomplished by providing support for a wide variety of protocols and data connectors that extend secure file sharing to meet the needs to share information internally systems as well as those of third parties.
Unified controls
Because secure file sharing ecosystems are comprised of information that comes from multiple sources, management can quickly become very complex. A secure file sharing system should have a unified view of all information and a centralized console for controlling and managing all aspects.
How to Securely Share Files Outside of Your Organization
A system for secure file sharing is designed to address the inherent risks posed by unsecured devices and tools. To be effective and ensure optimal usage, a secure file sharing solution needs to have robust security that protects data at rest and in transit. It also should have functionality that makes it easy to use and able to facilitate collaboration between internal and external users.
The following should be considered must-haves when thinking about how to share files outside of your organization securely.
- Advanced encryption for data in motion and at rest
- Advanced logging, reporting, and dashboard tools
- Process automation capabilities
- Structured user authentication
- Virus scanning and data loss prevention (DLP) features
Additional security features to look for when evaluating solutions for secure file sharing are as follows.
Technical security
Features that provide technical security are the ones that are built into a secure file sharing service’s software and programming, such as data encryption, multi-factor authentication, and access controls and management.
Audit logs
The purpose of audit logs is to provide a record of how files were used and who used them. Audit logs give administrators complete visibility into all activities and the ability to generate reports that can be used for internal purposes or to satisfy compliance requirements.
Audit logs also make users aware of their accountability and help reduce human factor security gaps, because they know that their activities are being tracked. Activities captured in audit logs include dates and times a user is logged in, files accessed, and actions taken, such as any edits or changes made.
Data encryption
Considered the most important security feature in a secure file sharing system, data encryption uses special algorithms to protect sensitive information by rendering it unreadable without a key. With data encryption, the content may not be viewed even if a file falls into the wrong hands. Data encryption protects sensitive information, whether it is being stored or transferred.
Document usage controls
In addition to being able to control access to files with permissions, administrators can also control what users can do with a document. For instance, secure file sharing solutions allow them to apply rules to a file that prevent a user from downloading or printing it. They can also make files and folders view only and prohibit any editing.
Human security features
The human factor is one of the biggest security gaps that organizations must address. Human-based security features help prevent unintentional risky behavior that could put sensitive information at risk. A Zero Trust security strategy that implements the principle of least privilege can mitigate human factor risks.
Multi-factor authentication
A layered approach to securing data and applications, multi-factor authentication is an access control system. Multi-factor authentication requires a user to provide a combination of two or more credentials to verify their identity in order to gain access—in this case, to access files.
Multi-factor authentication significantly enhances security and access controls because even if one credential is compromised, it is highly unlikely that unauthorized users will be able to provide the subsequent authentication requirements.
Permissions-based user roles
With permission-based user roles, system administrators are able to restrict access to specific folders and documents by granting or withholding permissions. Permission-based user roles allow administrators to limit access to a single document or folder related to a particular task or project.
This follows the principle of least privilege, which is a key part of a Zero Trust security strategy. It is often used in situations where multiple departments may need access to different aspects of data, but not the full data set.
Watermarking
A watermark is used to identify a document as sensitive. The watermark can be either visible and embedded into the document, or a digital watermark can be hidden and used for tracking purposes. Visible watermarks are added to address human security factors.
For instance, reminding users that a document is classified, contains sensitive information, or is for internal use only and is not to be shared outside of the organization. In some cases, a digital watermark contains personally identifiable information so that in the event that the document is printed or shared without authorization, the source of the unauthorized use of the file can easily be determined. Watermarking has been proven effective in deterring intentional or even unintentional sharing of sensitive information.
Secure File Sharing Delivers Benefits to Users and IT
To ensure data protection standards meet internal and external requirements, IT groups should provide a secure file sharing system to manage, track and govern the movement of information across systems, teams, and partners. If secure file transfer services are not provided, shadow IT will creep in and fill the gap.
Secure file sharing services are readily accessible, and most do not burden IT teams. Conversely, secure file sharing services punch above their weight in terms of value to the organization for productivity and a strong security posture.
Egnyte has experts ready to answer your questions. For more than a decade, Egnyte has helped more than 16,000 customers with millions of customers worldwide.
Last Updated: 9th January, 2023