Egnyte’s hybrid cloud solution can flex to meet your business needs, regardless of whether files are stored in the cloud, on-premises, or both. Learn more today.

Platform Architecture
Cloud Flexibility with On-Premises Performance
Don’t get “boxed in” to a one-size-fits-none approach. Built for the enterprise, Egnyte’s architecture can flex to meet your business needs, regardless of whether files are stored in the cloud, on-premises, or both. Improve business agility and cost efficiency while increasing security, removing vendor lock-in and maintaining data regulation compliance.

Extend cloud content to the edge
With Egnyte, teams working on large files – or at remote job sites with slow or inconsistent connectivity – can dramatically increase productivity by using a local storage appliance as their primary point of access. Egnyte automatically syncs back with a centralized cloud repository so remote users can always access the latest version of their files anywhere.
Leverage public clouds
Want to store, archive or access content from one or more of the public clouds (including AWS, Azure, and Google Cloud)? Egnyte’s public cloud integrations provide you with the maximum flexibility, control and ease of use. You can even build workflows that sync your Egnyte content to and from different clouds for processing and analysis.
Modernize legacy file systems
Preserve past investments while optimizing performance, improving user satisfaction, and lowering costs. Integrating on-premises file servers with Egnyte drastically reduces the money, time, and effort needed to manage and scale content processes. Eliminate the hassles of Distributed File System Replication (DFSR) and transform multiple servers into a single point of administration. Permission replication and file redundancy are built-in, meaning no more backup or disaster recovery expenses.
Meet data sovereignty requirements
Comply with data sovereignty requirements by keeping content in Egnyte’s US/EU data centers or a third-party cloud repository. Centralized trash management makes it easy to customize retention settings and comply with legal hold policies while centralized visibility and control of all company data makes compliance with industry regulations (GDPR, HIPAA, FINRA) simple.
Keep work flowing seamlessly
Egnyte integrates with all the most popular collaboration, workflow, CRM, and security tools. Share Egnyte files in Microsoft Teams, Zoom, or Slack, or link important documents in Salesforce or Docusign. Increase productivity without changing the workflows your people are accustomed to.
Integrate and extend the platform
Extract user records and related metadata from your Active Directory service into Egnyte. As new users and groups are created or deactivated within your AD, Egnyte will sync these changes. In addition, Egnyte’s API lets you extend content and granular access permissions to any internally or externally developed system. Build apps for custom workflows and content-rich business processes leveraging the full power of Egnyte.
Additional information
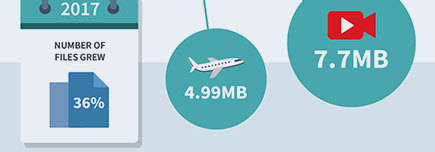
Businesses Are Looking Forward to a Hybrid Future
Egnyte’s team of data scientists analyzed 14 petabytes of data to see why hybrid (a mix of cloud and on-premises infrastructure) has become such a popular deployment model for businesses.

Buyer Guide: Moving to the Cloud
With so many options to replace legacy file management systems, how do you know which is right for your business? Download the buyer's guide to discover the right solution for your needs.
