What Is User Management?
For today’s hybrid-cloud enterprises, effective user management is critical. A robust user management system ensures the right people have the right access. As workplaces evolve with remote teams, SaaS sprawl, and tighter security needs, managing identities and permissions is more important than ever.
Let’s break down what is user management, why it matters now, and how modern user access control management can protect your data and drive operational efficiency.
Let’s jump in and learn:
Defining User Management
User management is a system to handle activities related to individuals’ access to devices, software, and services. It focuses on managing permissions for access and actions as well as monitoring usage. From onboarding and authentication to auditing and offboarding, user management includes:
- User access control management that aligns rights to roles or attributes
- Real-time visibility into user activity across platforms
- Compliance-driven management of credentials
- Keeping track of accounts related to software licenses throughout their lifecycle
Together, these user management tools form the backbone of a secure, agile enterprise.
Why Modern User Management Matters
Cloud apps, remote connectivity, and evolving regulations have raised the stakes. Modern cloud environments demand visibility across multi-cloud deployments. As a result, centralized user identity management has become essential for reducing risk and streamlining operations.
Without an advanced user management system, organizations risk shadow IT, compliance failures, and breach exposures. A strategic system with automated provisioning, seamless role changes, and audit trails keeps environments secure while supporting rapid business growth.
User Management and the Cloud
Cloud applications and resources require extra vigilance when it comes to user management. IT departments need to create and manage more complex policies to address the proliferation of accounts and the distribution of users.
To add to this complicated function, IT teams must track what type of user management system the various cloud service providers use. This is because user management in the cloud is handled differently depending on the type of deployment and the service provider.
Types of User Management Approaches
- Identity and Access Management (IAM): A broad framework for controlling who can access what, when, and under what conditions. It includes policies, authentication, authorization, and often integrates with directories and cloud services.
- Resource Access Management (RAM): Access policies are assigned at the resource level. It is commonly used in cloud environments to manage what users and systems can do.
- Directory-Based Management: Focuses on where user identity data is stored. Systems like Active Directory (AD) and Lightweight Directory Access Protocol (LDAP) serve as repositories that IAM solutions often rely on to manage user information.
User Management Software
User management software supports the authentication of users and storage of their data based on permissions and roles. APIs for user management software facilitate integration and streamline users’ access to applications. The user registration process, user authentication, and password management can all be handled through APIs. IT can also use consoles to manage all aspects of users’ accounts, including:
- Setting up user accounts
- Managing identities and application access
- Changing user properties
- Resetting passwords
- Disabling and decommissioning users
- Implementing multi-factor passwordless authentication
User management software can also be used to manage third-party accounts. For instance, partner accounts can be created or temporary access granted to vendors.
For SaaS, user management plays a critical role. Users, roles, and permissions must be tracked and carefully managed so that access is granted according to the terms of engagement.
Today’s user management tools can sync with directories, automate account setup through SCIM, and apply consistent access rules across cloud and on-prem systems.
Core User Management Features
Provisioning and deprovisioning: Automate onboarding/offboarding with role- or attribute-based access
Single Sign-On (SSO) and MFA: Enhance security and user experience
API integration: Seamlessly connect with cloud and on-prem systems
Session control and access reviews: Enforce timeout policies and periodic entitlement audits
Audit logging and reporting: Support compliance with GDPR, CCPA, SOX
License usage tracking: Optimize software licenses and reduce cost
Access request workflows: Streamline approvals with transparency
Passwordless options: Improve security and user satisfaction
Automating User Management
Automation now increasingly includes machine learning algorithms that detect unusual user behavior, flag risks in real time, and assist in fine-tuning access levels dynamically.
Technologies commonly used when automating user management include:
- Active Directory (AD): The standard for Windows domains, it syncs identities and enforces group policies.
- LDAP-based directories: Vendor-neutral, critical for Unix/Linux and mixed environments.
- SSO with JIT provisioning: Simplifies multi-app login and reduces identity sprawl.
- SCIM-based provisioning: Automates account creation/removal via standardized APIs.
- Zero-trust integration: Continuous revalidation of user credentials and permissions.
With each of these tools, user management can be automated, eliminating the need for cumbersome, error-prone manual systems. Some of the functionality that automated user management provides is:
- Access control based on role, department, location, title, and other attributes
- Access level changes based on the minimum requirements to perform job functions
- Audit trail of account activity for internal governance and compliance requirements
- Directory synchronization with applications, systems, and devices
Onboarding and offboarding users and roles
Benefits of User Management
User management software can help organizations gain productivity, security, and cost savings. Finance, HR, and IT all benefit from fewer security gaps, faster onboarding, and cost control across license lifecycles.
Productivity benefits with user management software
Automating user management with software saves time and increases efficiency by replicating changes made (e.g., creating, updating, and removing users) across systems. It also expedites the process of setting up users, roles, and groups, reducing workloads for admin teams.
Cost-saving benefits with user management software
User management software facilitates tracking of software usage to ensure optimal licensing. Licenses that are no longer needed can be reassigned. Agreements for software that is no longer needed can be terminated. Visibility into how many devices a user has activated under their license helps organizations optimize license distributions. It also helps with planning for future software budgeting.
Software license compliance benefits with user management software
With user management software, organizations can ensure compliance with licensing agreements by tracking users and their usage. This also simplifies reporting in the case of an audit.
Security benefits with user management software
User management software provides significant security benefits. By supporting strict access controls, unauthorized access can be prevented. In addition, the ability to quickly lock down or remove users helps mitigate risks from insiders. User management software also supports forensic audits for proactive security efforts, root cause analysis, and remediation in the event of a data breach.
The ability to enforce user access control management policies across cloud and on-prem environments further strengthens the enterprise security posture.
Conclusion
Understanding what is user management and implementing the right tools is now a top priority for any enterprise. With the right user management system, you can enable security, ensure compliance, and optimize cost. Modern user management software elevates your identity infrastructure from an obstacle to a business enabler.
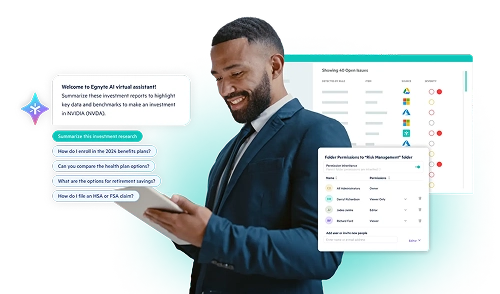
Egnyte’s governance suite integrates key components that support robust user oversight and user access control management:
- Seamless SSO support across multiple identity providers (e.g., Okta, Azure AD, Google)
- SCIM-based provisioning with Microsoft Entra ID for automatic user sync and deprovisioning
- Centralized dashboards for permissions and role management, with Governance Power Users to enforce and monitor access policies
These capabilities empower IT and security teams to prevent overprivileged access, minimize risk, and maintain compliance within Egnyte’s enterprise data governance framework.
Talk to our experts to learn how Egnyte can centralize user lifecycle, shield sensitive data, and streamline admin operations without introducing unnecessary complexity.
Frequently Asked Questions
Q. What is an example of a user management system?
Microsoft Active Directory is a widely used user management system. It lets organizations manage user identities, assign permissions, and control access to devices and applications across networks.
Q. What is user role management?
User role management assigns access based on someone’s job or responsibilities. Instead of setting permissions one by one, it groups users by role, like admin or editor, so they only see the tools and data they need. For example, a manager might have access to more features or data than a regular employee.
Q. What is user management in a website?
User management in a website controls how people sign up, log in, and interact with content. It sets rules for what each user can see or do, like viewing pages, posting comments, or managing their account settings.
Q. What is user management API?
A user management API helps developers handle tasks like sign-up, login, and role changes within their apps. It saves time by providing ready-made functions and ensures users get the right access across all connected systems.
Egnyte has experts ready to answer your questions. For more than a decade, Egnyte has helped more than 22,000+ customers with millions of users worldwide.
Additional Resources
User Management – Egnyte Help Desk
Find everything you need to manage users in Egnyte—from admin vs. non-admin roles, integrations, and ...
User Management in the Mobile Apps
Manage Egnyte users on the go—add, edit, or update roles directly from the mobile app.

Assigning Roles to Power Users
Create tailored roles to let Power Users handle specific admin tasks without full admin access. Simplify ...