Proactively Address Rapidly Evolving Cyberthreats and Manage Compliance Requirements
Secure your mission-critical content with a comprehensive governance solution.
Empower Your Data Governance
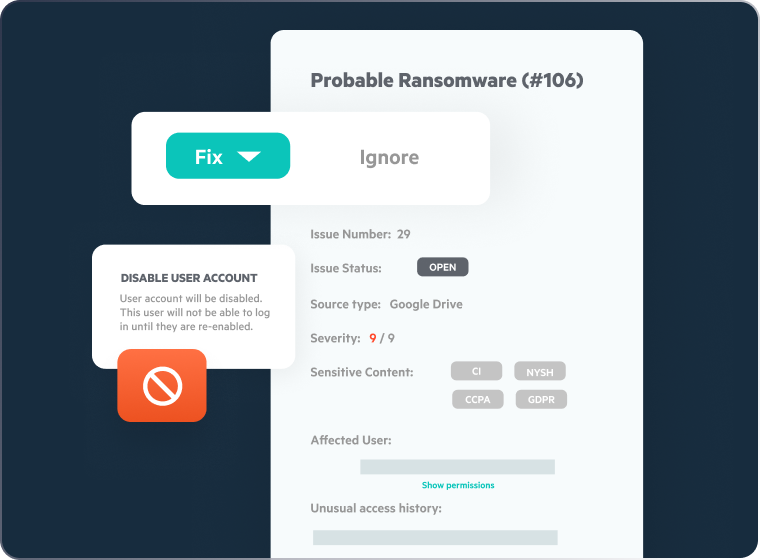
Defend Against Ransomware
- Proactively manage the threat of ransomware
- Detect known ransomware artifacts
- Keep pace with rapidly-evolving ransomware variants
- Take immediate action when users experience attacks
- Recover quickly from successful attacks using Snapshot Recovery
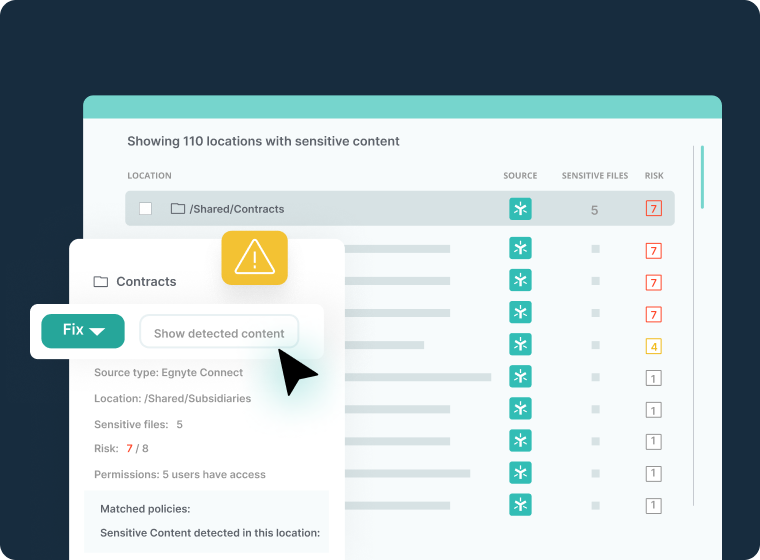
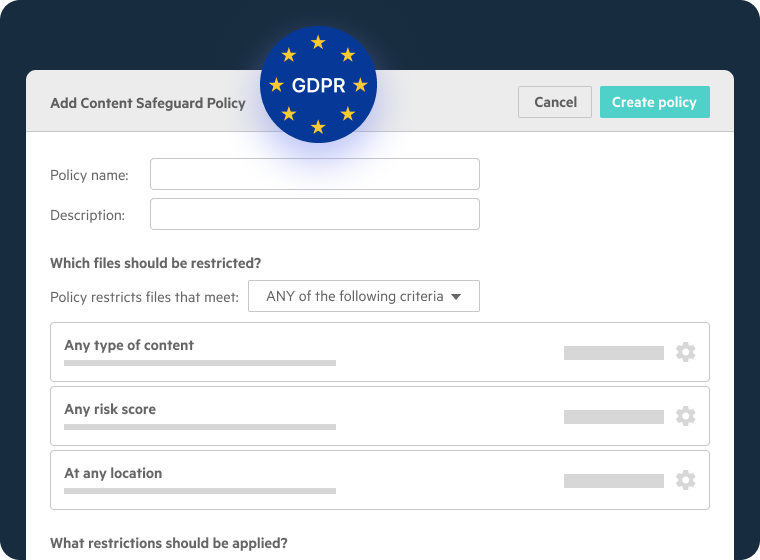
Protect Sensitive Content
- Identify and review sensitive content including Personally Identifiable Information (PII), Payment Card Industry Data Security Standard (PCI-DSS) data, and Controlled Unclassified Information (CUI)
- Take immediate corrective action to protect exposed data
- Strengthen your compliance with global data privacy regulations such as GDPR and CPRA
- Continuously improve sensitive data protection
Manage Regulatory Compliance
- Comply with cybersecurity and data privacy standards, such as CMMC, ISO 27001, and the CPRA
- Detect data that’s subject to compliance and data privacy standards
- Keep pace with rapidly-evolving international privacy and cybersecurity standards
- Benefit from Egnyte’s deep compliance experience
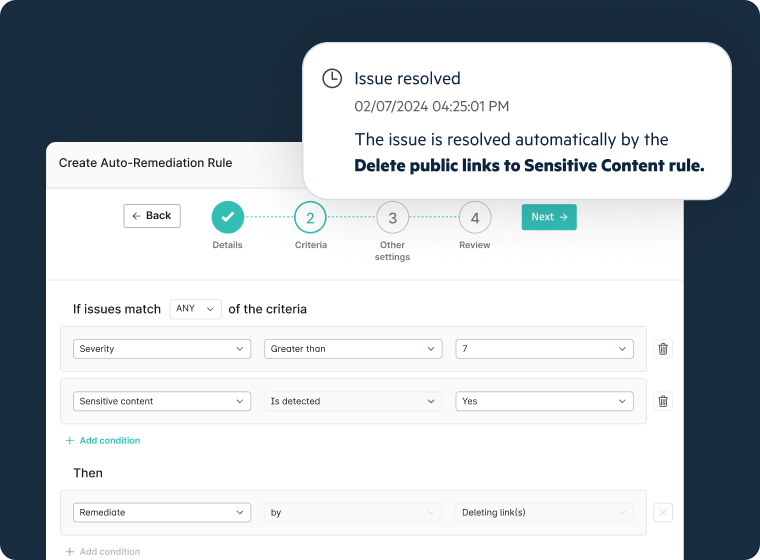
Remediate Security Issues
- Mitigate risk associated with common security vulnerabilities like publicly exposed document links and potential ransomware
- Automatically respond to suspicious Egnyte login attempts
- Enable your team to focus on threats most likely to significantly impact your company
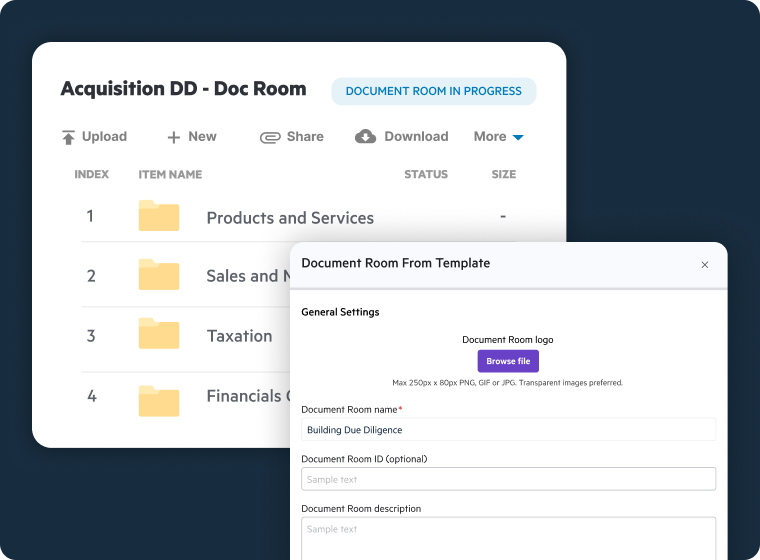
Keep Data Confidential
- Create virtual data rooms (VDRs) for secure collaboration with external entities
- Generate Document Rooms in support of M&A, asset sales, and investment fundraising initiatives
- Watermark previewed files to limit the risk of data breaches
- Gain real-time insights into users’ document access activity
- Terminate external entities’ access when projects are completed, for peace of mind
Hear From Our Customers
See Egnyte’s Data Governance In Action

Learn how easy it is to manage your mission-critical data privacy and compliance projects with Egnyte.
You Might Also be Interested In
FAQs
Controlling access to PII and other sensitive data requires automated discovery, classification, and policy enforcement, manual processes cannot keep pace with the volume of content organizations generate. Platforms that automatically scan repositories to identify PII, PHI, PCI-DSS, and CUI give security teams a clear picture of where sensitive content resides. Once classified, granular access controls and role-based permissions ensure only authorized individuals can view or interact with sensitive files, while sharing restrictions prevent external exposure. Real-time alerts notify administrators of unexpected access patterns, enabling immediate corrective action and supporting compliance with GDPR, CPRA, and HIPAA.
Ransomware protection requires a proactive, multi-layered strategy combining early threat detection, access controls, and rapid recovery, relying solely on endpoint security or backups leaves organizations exposed to extended downtime. Effective platforms monitor for ransomware artifacts and behavioral signals, such as mass encryption or unusual access patterns, before an attack can spread. When detected, automated responses including user suspension contain the blast radius and limit the number of files affected. Snapshot recovery enables organizations to restore large file structures in minutes rather than hours, dramatically reducing recovery time and business disruption compared to traditional backup-and-restore processes.
Insider risk, from malicious actors, negligent employees, or compromised accounts, is difficult to detect because the access is often legitimate. Effective governance platforms continuously monitor user behavior across the file system, flagging anomalies such as unusual download volumes, sharing to external parties, or access outside normal working hours. Automated remediation capabilities allow administrators to respond immediately, restricting access, revoking sharing links, or suspending accounts, without waiting for manual investigation. Role-based access controls and the principle of least privilege limit the potential impact of any single compromised account, while detailed audit logs provide the forensic trail required for incident investigations and regulatory reporting.
Granular access control means defining precisely who can access, share, download, or modify each piece of content, a capability that becomes essential as organizations scale. NTFS-style folder permissions allow administrators to configure access at the user, group, or role level, with overrides for individual files or subfolders where needed. View-only permissions prevent downloading or printing; link-based sharing can be password-protected, time-limited, and scoped to specific recipients. These controls are enforced consistently across web, desktop, and mobile interfaces, ensuring permission policies hold regardless of how a user accesses content. For regulated industries, this access model aligns with SOC 2, HIPAA, CMMC, and ISO 27001 requirements.
Meeting overlapping regulatory frameworks requires continuous scanning of content for data types subject to specific regulations, PCI-DSS payment card data, GDPR and CPRA personal data, HIPAA health information, and SOX-relevant financial records, surfaced in a centralized compliance dashboard. Policy-based automation allows organizations to take immediate corrective action when regulated data is found in the wrong location or shared beyond permitted scope, reducing the window of exposure. Comprehensive audit logs track every file access, modification, sharing event, and permission change, providing the documentation auditors require to verify that compliance controls are operating effectively.
As organizations adopt generative AI tools, one underappreciated risk is enterprise file content being used to train external AI models without consent. Consumer AI tools may retain prompts and uploaded documents as training data, meaning a single employee uploading a confidential contract could embed that content in a public model. AI safeguard capabilities address this by classifying sensitive content, restricting sharing to unapproved AI destinations, and ensuring AI tools only access content the user is already authorized to see. Connecting approved AI assistants, such as Claude or Microsoft Copilot, to company data through governed APIs enforces existing permission models so no AI tool ever accesses more data than the user it acts on behalf of.
Sensitive data discovery is the foundation of effective governance, organizations cannot protect data they cannot find, and legacy file systems often contain years of unclassified content across multiple repositories. Automated classification solutions scan repositories to identify PII, PHI, PCI-DSS data, and CUI, surfacing findings in a centralized dashboard with context on file location, data type, and exposure risk. Unlike point-in-time audits, continuous scanning ensures sensitive data introduced after the initial assessment is captured immediately. Findings can trigger automated remediation, restricting access, applying retention policies, or flagging content for human review, reducing manual effort and accelerating compliance risk reduction, particularly for organizations migrating from legacy infrastructure.