Classify Data by Sensitivity Levels for Better Governance
All organizations, including yours, have sensitive data. Whether it’s structured or unstructured, you need to protect that data to avoid disruption to your business.
However, data sensitivity classification is not binary—it requires a more nuanced approach.
Some information is more sensitive because it creates greater risk of harm to the organization or customers if it’s exposed. Highly sensitive data, for example, needs protections that may require additional technology and processes. Smart organizations perform risk analysis on various types of data so they can intelligently choose the appropriate level of protection and governance for each type of data.
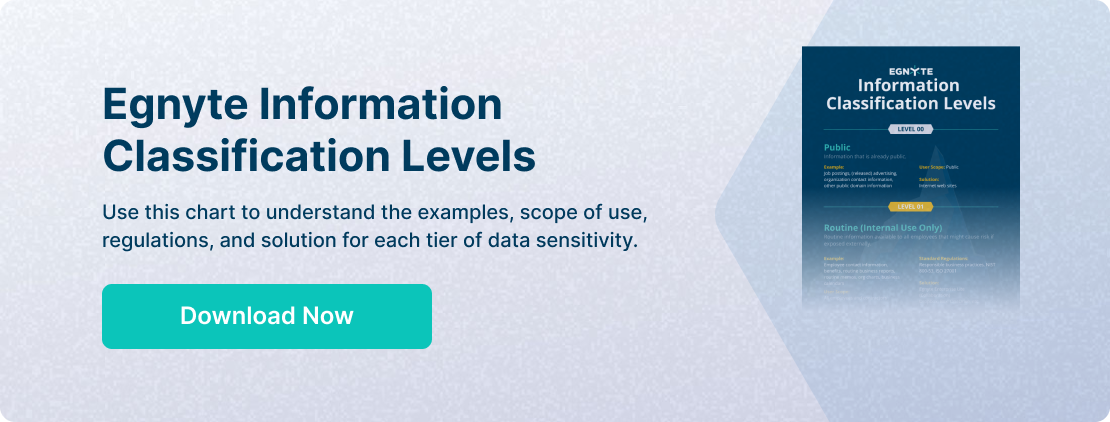
Egnyte has developed information sensitivity classifications to help its customers understand the various levels of sensitivity and associated controls. Using the descriptions in this blog and the corresponding chart (follow the link below), you can make general observations about which information deserves more governance.
Level 0
The least sensitive data is data that is already public, or data that wouldn’t pose any risk to the organization if exposed. In fact, this data is most valuable when it's public, like when a company posts a job opening to solicit applicants.
However, the organization is still responsible for the accuracy of its public information. In some cases, there are legal requirements to protect the accuracy of information such as financial disclosure filings. Therefore, data integrity should be preserved by keeping master copies of downloadable documents in a secure place to recover them if needed.
Level 1
The next level of sensitivity is for data that the organization would prefer to keep private but probably wouldn’t cause risk or damage if exposed. Such data is freely available to all internal employees and includes company calendars, professional contact information, etc. It also includes company policies, processes, and organization charts.
Many organizations also include routine office memos in this category. Egnyte customers routinely store this level of information in third-party repositories such as Google Workspace, Microsoft 365, Dropbox, and Box. However, there is no need to migrate data to one central location to monitor it. Egnyte can monitor these repositories to discover and classify more sensitive information and alert you to risks.
Level 2
This next level is where security experts are more cautious. Exposing this information could put the company at risk and cause material harm. Access is typically limited to a small number of employees who need the data to do their jobs. It’s often isolated by department, which means the exact type of information will vary depending on their specific needs.
A development team may hold roadmaps, product designs, and source code in this category. Financial teams keep pricing plans, purchase contracts, margin analysis, etc. Sales teams hold customer PII as well as sales contracts in this category.
This is where moving to Egnyte for classification and governance of sensitive information really makes sense. Egnyte’s tools help to protect this information and automatically generate prioritized alerts upon detection of issues.
Level 3
This data is typically only accessible to company leaders, accounting and finance, and legal counsel. Examples include merger and acquisition data, funding rounds, and critical contracts. Because exposure could cause an existential threat to the organization, most employees are never aware that it exists.
This type of information is typically protected with additional technology, processes, and procedures, so some Egnyte customers set up additional tightly controlled Egnyte domains for this type of information.
Level 4
Because it deals with government contracts, this level of information is critical not only to the organization but also to national security to some extent. For companies working with the United States Department of Defense, this is defined as Controlled Unclassified Information (CUI). This data is sensitive because exposure could lead a nation-state adversary to draw conclusions about U.S. defense plans.
It includes product specifications, but also contract terms and schedules for delivery. Governed by the NIST 800-171 standard and CMMC requirements, this data can be supported in a special environment by Egnyte. Egnyte can also scan all other repositories for ITAR-related information and custom keywords to avoid leakage of this information into other areas. Contact your Egnyte representative for details.
Level 5
Finally, this level includes government classified information. This is information that a government has deemed to be so sensitive that its disclosure could threaten national defense and security.
It’s usually well marked and kept in air-gapped systems. Although Egnyte does not support this level of sensitivity, Egnyte tools can be used as a backstop to discover when this information has been leaked into lower-level systems so it can be removed.
Learn More
By developing a hierarchy of data sensitivity levels, you'll be better prepared to govern your data and find the Egnyte solution that fits your needs. For more information, click here to download an infographic you can use a reference point for your own analysis. For each classification level, you'll find corresponding examples, scope of use, regulations, and the Egnyte solution.
If you have further questions about how Egnyte can protect your data, reach out to your Egnyte representative for more information and a product tour.