The Permissions Fiasco: Deconstructing Consumer-first File Sharing Solutions
In an article recently published on CloudTweaks, Egnyte’s Chief Customer Officer Rajesh Ram discusses five key considerations for businesses evaluating file sharing solutions.The first of these five considerations, which is often overlooked, is whether the file sharing solution was architected for businesses.There are two categories of enterprise file sync and share (EFSS) solutions. The first consists of solutions that were built for individual users and then adapted for businesses - let's refer to this category as ‘consumer-first’. The second category comprises solutions that were built from the ground up for businesses - let's refer to this category as ‘business-first’.Consumer-first architectures pose numerous challenges for business, a significant one being a broken permissions model.The Permissions Problem If you’re an IT professional that's been around the block for a few years, you understand how enterprises handle permissions on file servers. Individual users may each have a home or private folder that only they can access. Then there’s a shared hierarchy of folders, and users or user-groups have varying levels of access to folders in the hierarchy.
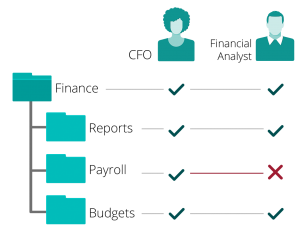
Figure 1. The need for unique permissions for subfolders. Subfolders inherit user permissions from their parent folders by default, but inherited permissions can be overridden as needed.When your business moves to a cloud-based file sharing solution, you may rightly expect your cloud infrastructure to mimic the file server permissions model. However, with Consumer-first file sharing solutions, you’d run into problems.Take vendor B, for example, who implements a ‘waterfall’ permissions model that does not allow inherited subfolder permissions to be modified.Imagine you’re the CFO of a company. You obviously need access to the top-level Finance folder and all its nested subfolders, including those that contain sensitive payroll information. No problems so far. Then you hire a financial analyst, who should be able to access the Finance folder and all its subfolders except a few like Payroll that contain sensitive, confidential information (figure 1).You can't do that with vendor B. Because it does not allow for the Payroll subfolder to have different access permissions than its parent Finance folder, for a given user. As a workaround, subfolders requiring unique user permissions have to be moved to the top of the folder hierarchy, which creates more problems. Users now have to deal with a top-heavy hierarchy and lose track of the positional relationships between these folders and their former parent folders. Modifying folder hierarchies (figure 2) to accommodate the limitations of vendor B results in lost productivity for both users and administrators.
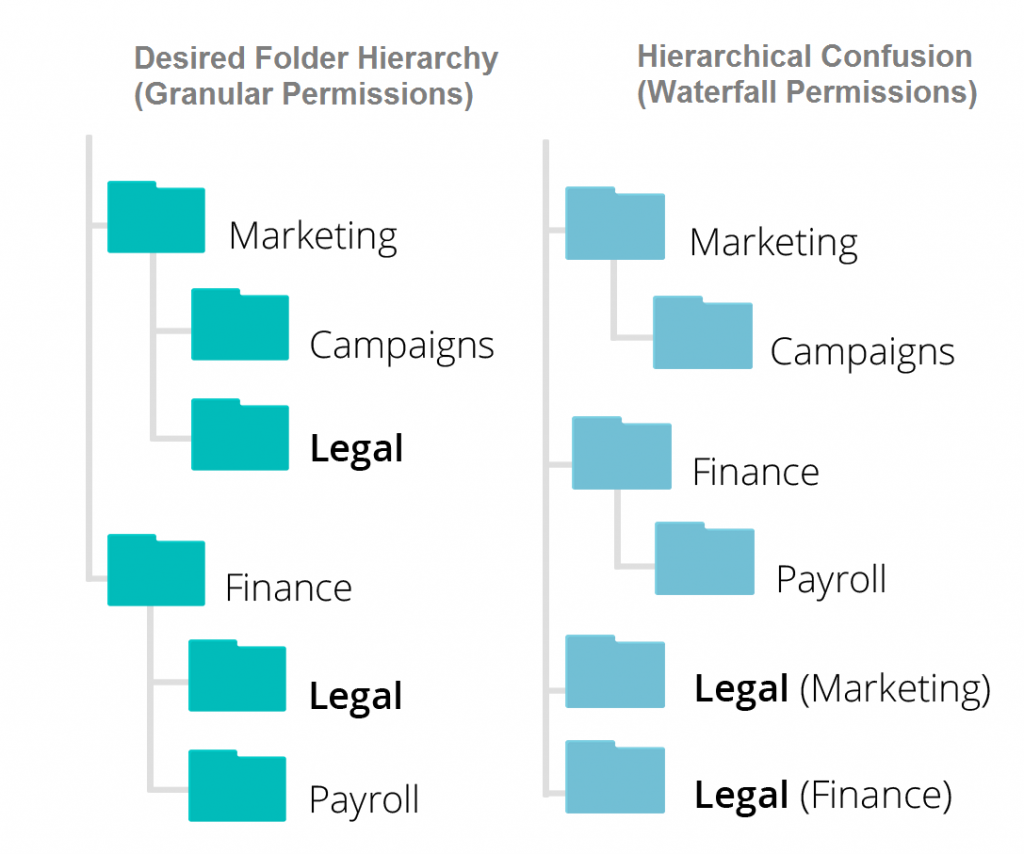
Figure 2. Desired folder hierarchy compared to modified hierarchy in consumer-centric solutions Now magnify the impact of these challenges to thousands of users, tens of thousands of folders and millions of files, and you can see how the entire file sharing infrastructure begins to crumble.It's probably intuitive that many users are incredibly frustrated with such a permissions model. To quote a few users from vendor B’s user community site:
"I had plans of doing some very useful things in B but this rigid 'Waterfall' structure is basically a deal breaker.""B is being marketed as an enterprise level sharing/collaboration tool, yet it doesn't seem to accommodate enterprise level complexity with regards to permissions/authority over content. Why?""What I do not want is users to log in and have dozens of folders at the top level. This is already an issue for us with B."
This is a short extract from a very long list of complaints.Users of another vendor, D, suffer a similar fate. Quoting vendor D’s users from its community pages:
"I absolutely agree that it should have this feature. I paid for D for Business thinking I was getting the ability to control what is shared. I need to be able to share my entire project directory with some people, and only subfolders with others.""I'm pretty sure nobody will switch to D PRO knowing that you cannot share to a different user a subfolder of an already shared folder...this limitation needs to be addressed ASAP, or D would be kicked off from cloud drive markets soon.""I am a new D for Business customer, and I am frankly shocked that this is an issue. This is a basic function [...] not being able to have shared folders within shared folders makes file structures infinitely more difficult to keep track of. This makes no sense in virtually any corporate environment. This is a critical problem that needs to be fixed if D plans on adding many corporate clients in the foreseeable future (including my organization, I might add)!"
Again, this is just an extract from a long list of complaints.The Root of the ProblemThe Permissions problem is just one of many that result from architectures that were created for individual users, rather than for businesses. How are Consumer-first file sharing architectures different? They lack a shared enterprise content repository. In a Consumer-first file sharing architecture, content resides in individual user account silos. These silos are loosely patched together with single sign-on and administration APIs when the vendor rolls out a ‘For Business’ offering.

Figure 3. Consumer-first file-sharing solutions: a collage of individual accounts creating islands of content The absence of a centrally managed repository also creates numerous administrative challenges, and limits the ability of the vendor to roll out a rich enterprise feature-set.Overcoming the Permissions ProblemThe only real fix for the permissions problem, and other problems resulting from Consumer-first file sharing architectures, is to switch to a Business-first File Sharing solution.
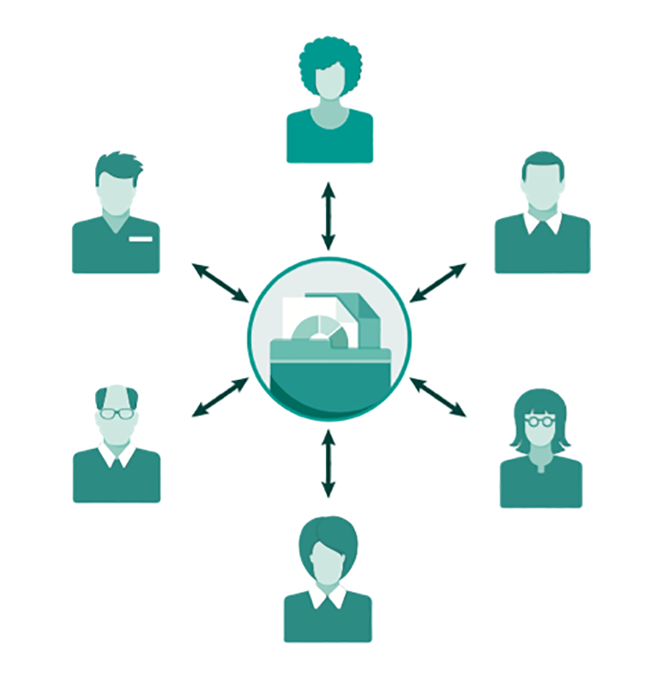
Figure 4. Centralized, scalable, robust and secure Business-first file sharing solutions have a centralized content repository which provides a shared, hierarchical frame of reference for all users. Access to content is managed with a file-server like permissions model, which simplifies administration. Users access content residing both on the cloud are on premises with consistent and intuitive workflows that improve productivity.Business-first file sharing solutions support essential enterprise features like granular subfolder permissions, external user accounts and comprehensive audit trails. They are architected from the ground up for robust security, performance and scalability.For more information, visit egnyte.com.