All The Permissions You Need...Without Having To Ask
Easy for IT
They are the overseers, network managers, and implementers of corporate policy. When it comes to day-to-day operations, IT admins configure and upkeep company file servers and collaboration applications. This is no small feat, especially when it comes to ensuring data privacy across an organization.
Safeguarding sensitive information, regulated data, and intellectual property is crucial to protecting business reputation, compliance, and productivity. Reliance on consumer products can pose serious security risks by limiting IT’s ability to manage content, as well as restrict an organization’s collaborative capabilities. The better approach is a true enterprise-grade solution that offers robust access controls for corporate data. If you’ve ever used a Windows file server, you’ll know what how valuable this is.
Granting Permission
In order for admins to do their job effectively, IT needs total content visibility and access control. They should be able to give Gerald in R&D access to his Data Collection folder and restrict his access to the Research Budget folder in just a few clicks. Egnyte Connect makes it easy for admins to set permissions so that users/groups only have access to the content they need. Our enterprise solution offers the ability to add, remove, or change access permissions for all users, folders, and subfolders.
We do Granular Better
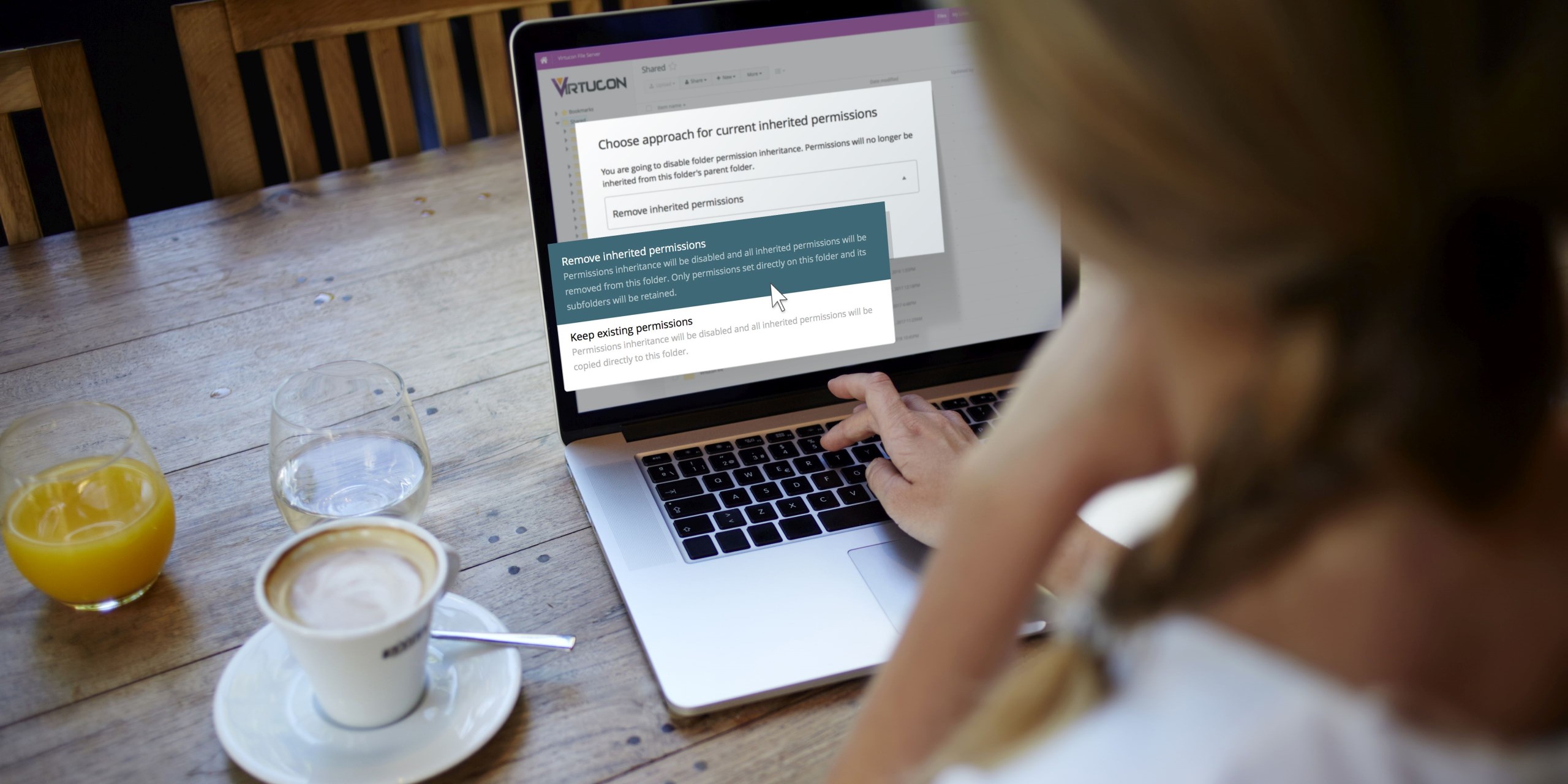
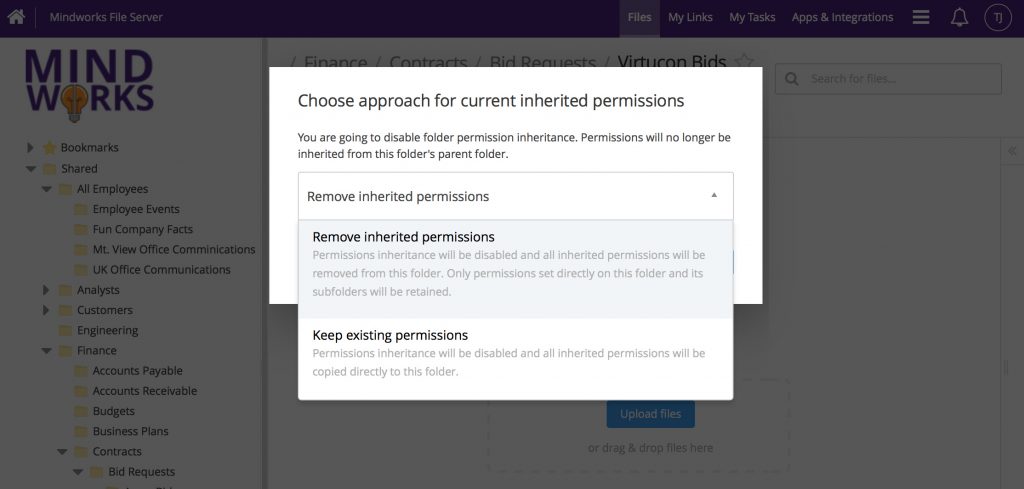
Regardless of your company’s size and structure, Egnyte provides options for setting folder permissions in three ways; inherited, inherited with manual override, and non-inherited.
A folder with inherited permissions clones privacy settings from its parent folder. Think of inherited permissions as a top-down approach, which grants all users with access to the parent folder access any folder added beneath it. (Most consumer-grade solutions stop here)
But what if you want to change access for just a few individuals? Inherited permissions with manual override lets owners and admins add and remove specific permissions for users/groups in any folder. Overriding permissions can be especially useful when updating a user’s access level, like changing to read-only or removing access altogether.
However, this method doesn’t always scale. If users are added to a parent folder, they will be automatically inherited by its subfolders, even those with restrictions. Maintaining data privacy with this method requires having to override permissions in every folder for each additional user, which can be cumbersome.
Often, an easier way to control access, especially for highly sensitive data, is through non-inherited permissions. With this method, permissions aren’t carried over from the parent, so the folder effectively behaves like a root-level folder. An admin will explicitly grant access to those who require it, restricting everyone else by default. Think of this as a bottom-up approach –– even if permissions are changed above, the non-inherited folder won’t be impacted.
Data privacy requirements may differ by department and industry, but the ability to set granular folder permissions helps companies maintain security. Businesses need a solution that puts their interests first. This means a system that has been purpose-built to give them complete control of how their data is handled by all users and devices, both inside and outside the organization. Our unique enterprise architecture provides end-to-end data protection, which makes IT’s job easier, so end-users can work better. Click here to learn more.