File Sharing IT Teams Prefer. And Users Love.
- Single point of administration for fast and easy control
- Share files securely from anywhere, any time on any device, without a VPN
- No more bandwidth limitations or email attachment restrictions
- Rapid ransomware detection, remediation, and recovery
* No Credit Card Required


22,000+ Businesses Share Files Easily and Safely
Enterprise-Grade Security Plus A Great User Experience
Enjoy secure file sharing across web, mobile, and desktop environments, simplified administration, and robust ransomware protection—all in a single platform.
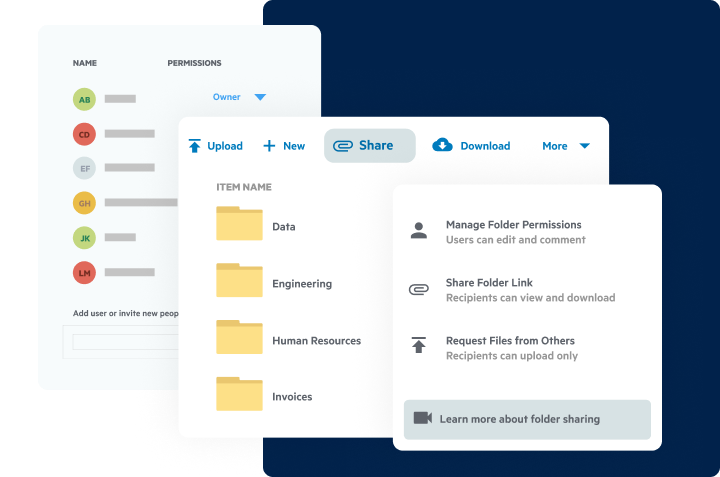
Share Large Files In Seconds
- Secure link sharing eliminates email attachments and FTP, even for the largest files
- Password-protect any file, automatically expire access, and securely collect files from users outsider your organization
- Scan all incoming and outgoing files for ransomware signatures, sensitive, and regulated data

Work Securely On Any App, Any Device, Anywhere
- Create and share files in any browser, desktop, phone, or tablet without VPN
- Combine the reliability of the cloud with the familiar user experience of a local hard drive
- Safely create, co-edit and share using your favorite productivity tools, like Microsoft 365, Google Workspace, Slack, DocuSign and hundreds more
A Single Pane of Glass to Monitor and Control Content
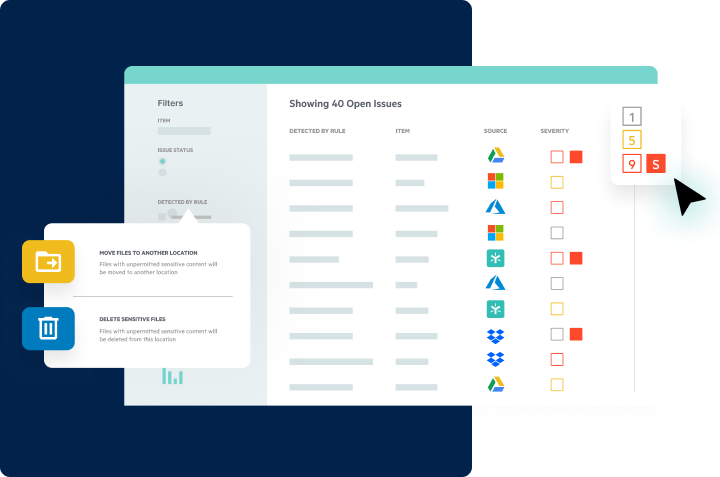
- Locate and manage sensitive data in any repository, including Egnyte, OneDrive, SharePoint, Exchange, Box, Google Workspace, Gmail, Dropbox, and more
- Centrally monitor permissions and decide which users can access and share high-value and regulated files
- Get rapid alerts for known and suspected ransomware, suspicious file sharing, and high-risk user behavior
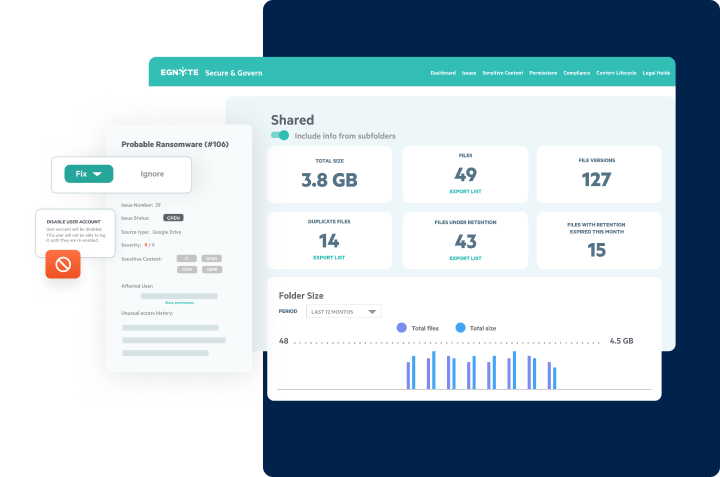
Detect, Alert and Recover from Attacks Quickly
- Continuously monitor sensitive data with a combination of behavioral and signature-based detection
- Get alerted to potential data compromise in order to remediate quickly
- Speed investigation with an audit trail of compromised users, files, and sensitive data
- Recover with precision by selectively restoring files and their associated permissions and metadata, across your entire organization
ADVANCED SECURITY & GOVERNANCE
Gain Full Visibility And Control
Without Third-Party Governance Tools
‘Smart’ reporting & auditing
- Access automated reports built with historical file and user statistics
- Monitor key usage details, like access permissions, login insights and active sharing links
- Run one-time reports or set them to run on a recurring schedule
Granular sub-folder control
- Grant or restrict any users access to any folder or subfolder
- Disable folder inheritances for any sub-folder
- Set access permissions at the individual and group level
Unified Administration for Multiple Domains
- Single administration point for all domains
- Only see domains you have credentials for
- Maintain full customization per domain as needed
Custom Classification policies
- Search, discover and classify sensitive and regulated data across the company
- Automatically enforce policies to prevent unauthorized sharing of sensitive content
- Choose from pre-built classification policies or create your own based on your business needs
AUTOMATED LIFECYCLE MANAGEMENT
- Set custom retention, archival and deletion policies to manage sprawl and reduce attack surface
- Review or restore previous file versions with the click of a button
- Full visibility into when files are restored and who restored it
Role-based administration
- Grant select users administration rights
- Keep granular control over what admin functions are given, such as granting billing access to the finance team
- Retain full visibility into when every change was made and who made them

PC Mag
“Egnyte is one of the strongest offerings on the market.”

Gartner Peer Insights
“Gartner Peer Insights Customers’ Choice Winner for Content Collaboration Platforms”

G2
“A Leader in File Storage and Sharing for 2024”

Forrester
“390% Average Return on Investment (ROI) When Deploying Egnyte”



